Avast Antivirus is the most famous Antivirus in the world. It is so popular among PC users because it offers both a Free Version and a Premium Version, which can be used in computers such as desktops and laptops. There is an Android version of this application as well. If you are not so tech-savvy, let me first tell you in short what Antivirus is.
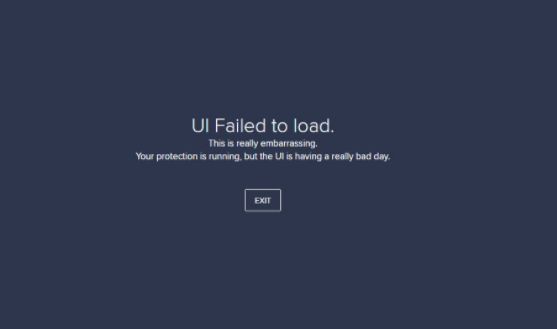
An antivirus is software that protects your system from viruses, malware, and Spyware. Ever since the Windows 10 update, people have been reporting that they are getting an error message saying Avast UI failed to load.
Windows is infamous for providing buggy updates. The same thing was reported in Windows 7 as well as Windows 8. It's quite sad to see that Windows, even after becoming the most used Operating System on the planet, has failed to achieve proper security, and adding to that, most of their updates are quite buggy.
However, they fix the bugs in later updates. But the avast UI failed to load has been bothering people for quite some time now. In this article, we will suggest a few troubleshooting methods, following which you can sort out the issue.
What Causes Avast UI Failed To Load?
Here are some of the root reasons listed below for this error.
- There is a good chance that this error pops up because of some error in the configuration of Windows.
- Another reason for showing Avast UI Failed to Load pop up is that you might be using more than one antivirus simultaneously on the same device.
- The last reason we could think of is if there is any problem with your system's Remote Desktop Services.
How Can You Fix Avast UI Failed To Load Issue?
In order to fix the "Avast UI Failed to Load" issue, you need to check a few things first. Make sure that you have exited the Antivirus. Restart Avast Antivirus. But still, if the issue is not fixed, you can follow these procedures to say bye-bye to this issue.
Procedure 1: Turn On The Remote Desktop Services
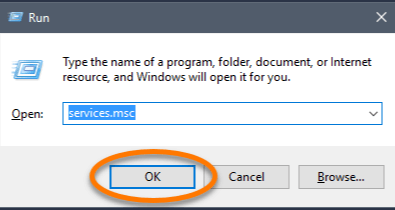
What you need to do is press the Windows key and R simultaneously. This will open up the RUN box.
After having that box on your screen, you have to type 'services.msc' in that box and press the enter key.
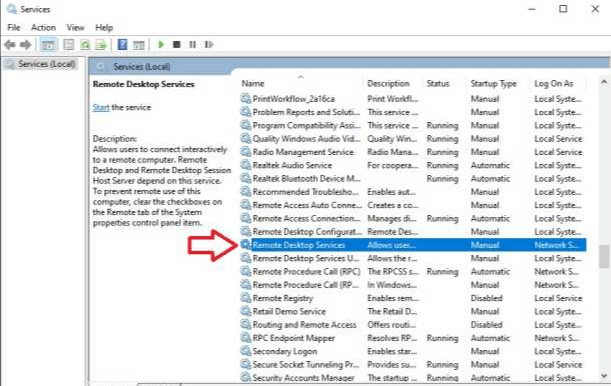
Now check for the Service Page. After finding the Service Page, you have to search for Remote Desktop Services. After you have found the remote desktop services, what you need to do is right-click on it and then select the option of 'Properties.'
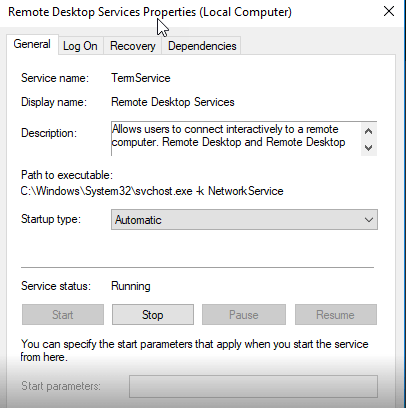
After clicking on properties, you have to double-click on the button that says start and set the startup type to automatic. After you have done that, click on 'OK" to confirm the changes you have made. Now, you have to close the services page and manually restart your PC, laptop, or whatever you are using. It will complete the process. If you are still facing Avast's problem, UI failed to load, then kindly follow the next procedure closely.
Procedure 2: Try Repairing The Avast Antivirus Software
Kindly follow this procedure closely to repair. You have to go to the Control Panel Section. You can find the Control Panel in the settings section of your computer. If you do not know how to open the control panel.
Click on the start button and type the control panel. After opening the Control Panel, search for the Program & Features option, find it, click on it, and look for Avast Antivirus software. Now, you need to right-click on Avast; you will get the option to uninstall/change.
Be very careful while doing this, as a single mistake can uninstall Avast from your PC. Select the option to repair after having clicked on change. Now, you need to wait for Avast to repair itself, and after Avast completes its repair, reboot your PC. If the error of avast UI failed to load persists, kindly follow the next procedure.
Procedure 3: Uninstall And Reinstall Avast Antivirus Software
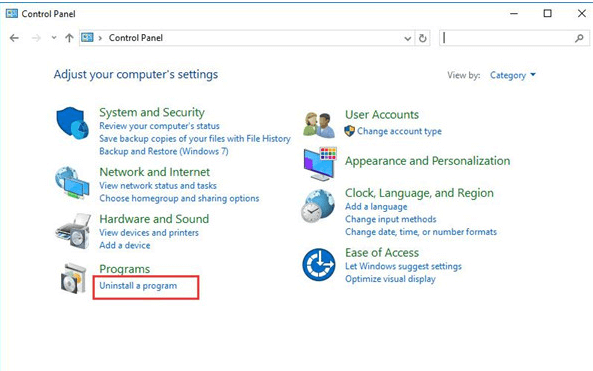
If any of the above methods did not work for you, then you try to uninstall Avast Antivirus. To uninstall Avast Antivirus Software, you need to open the Control Panel. You can open Control Panel by merely typing Control Panel in the Run dialog box; another way to open Control Panel is by searching the control panel after clicking on the Start button.
After opening the Control Panel, go to the programs and features section and find the Avast Antivirus software. Right-click on it and select uninstall this time instead of selecting change as you did in the previous procedure.
Please wait for some minutes for Avast Antivirus Software to completely uninstall itself from your computer. Reboot your computer as the final step of the process. Switch back on your computer, download Avast from the official website, and install it again as a whole new software.
Make sure you do not do anything else on your computer while Avast Antivirus is being installed, as it puts extra pressure on the computer's RAM. After the installation process, open Avast and check if the Avast UI failed to load the error persists. If it does, kindly follow the next procedure.
Procedure 4: Get The Recognition Issue Fixed
If the error of Avast UI failed to load persists, you could follow the last and final procedure.You need to look up from the Avast icon on your desktop and Open the shield's control. In shields control, right-click on the Disable to disable the shields. You will get the option to disable it for 10 minutes to an hour. Disable it for 10 minutes, wait for 10 minutes, and check if the 'avast ui failed to load' issue persists. If the error is still showing, then try out some other methods.
- Press the Windows Button and R buttons simultaneously. It will open up the Run dialog box. Type cmd in that box so that it opens the Windows Command Prompt Box. Type 'winmgmt/verifyrepository' on the search field and hit the enter button.
- If it shows the status as inconsistency, you need to type 'winmgmt/salvagerepository' in the search field and press the enter key to finish the process.
- If the result shows that the Windows management instrument was consistent, you need to type 'winmgmt /resetrepository.'
- After doing that, Windows will send you a message showing that the WMI repository has been rebuilt successfully.
Finally, you need to reboot the system and start Avast antivirus, and hopefully, it will not show the error of Avast UI failing to load. We are sure that after trying all these steps, your Avast Antivirus will run just fine. But still, if the error exists, we suggest you contact Avast Customer Care as soon as possible.
Procedure 5: Update Your Avast Software
Most of the time, what can fix such an error message is a simple update. Fortunately, you can update the app without the hassle of having to re-download the app. Redownloading can be a viable option if you cannot access the interface at all. Here is how you can update Avast Antivirus as well as other Avast applications that offer easy updates to its users.
- Press the Windows+X keys at the same time, then select the app and features from the context menu.
- Find the Avast Antivirus or any other app that is causing you to see the UI failure arrow. Click on it, and from teh options that unfold, choose Uninstall.
- Click the Update button and wait for the software to locate any new updates that might be ready to download. It will automatically install the latest version, which will take quite a bit of time, depending on the configuration of your system.
- When the repair process is complete, launch the Avast app that you were having trouble with. This should get your app up and running.
It is possible that updating the Avast app the way mentioned above will fix the internal corruptions or missing files, thereby restoring the UI. But if you are still facing the same issue, try speaking to Avast Customer Support.
Conclusion
Avast is one of the best antiviruses in the market. The story of avast goes way back to 1995. Initially, it did not offer the best of services, but they have been improving their services year by year. It's one of the few antiviruses that offer a premium version and a free version as well.
Do not think that the free version has limitations like other antivirus software because it's not so. The free version provides a few premium features, which include a WIFI inspector and ad blocker, etc.
However the recent trend of Avast showing that the Avast UI failed to load is not what users are expecting. Whether it's the fault of Avast or Windows 10 is yet to be found out. Rest assured, you can try the above procedures to get rid of the issue.























