Stellar Data Recovery Professional For Mac
 If you wish to recover deleted or lost Word, PDF, or Excel files from your Mac, Stellar Data Recovery is the best software for you.
If you wish to recover deleted or lost Word, PDF, or Excel files from your Mac, Stellar Data Recovery is the best software for you.
- With the help of Stellar Data Recovery Professional for Mac, you can recover data from the lost volume and crashed and non-booting Mac.
- Not just this, with this software, you can also monitor the health of your hard drive
- This software also allows to perform disk imaging and disk cloning.
Tenorshare 4DDiG (Mac)
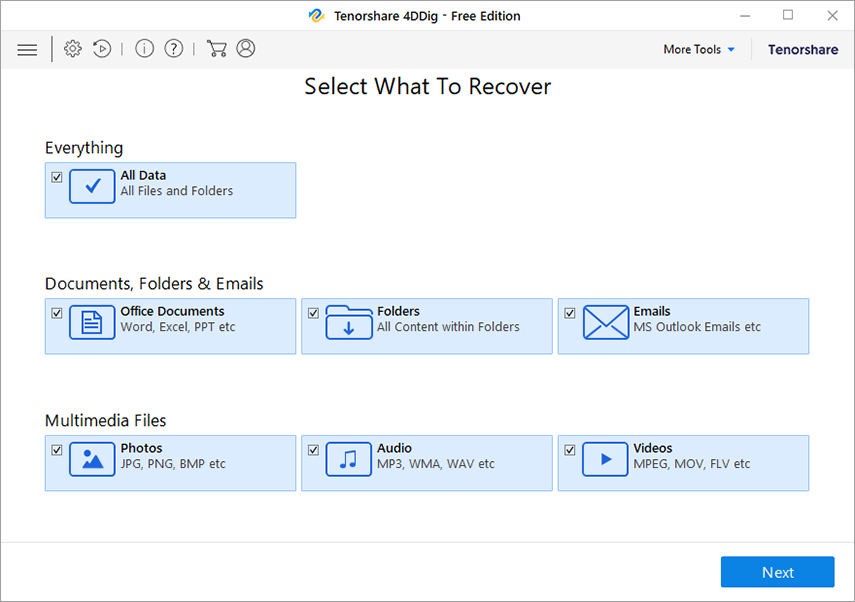 It is a powerful Mac data recovery software that allows users to recover unlimited photos, videos, documents, audio, etc., from Mac and external storage devices that are lost, deleted, or formatted.
Tenorshare 4DDiG (Mac) also allows raw recovery, lost file recovery, and partition recovery. You can even recover data from crashed or dead Mac using the software.
It is a powerful Mac data recovery software that allows users to recover unlimited photos, videos, documents, audio, etc., from Mac and external storage devices that are lost, deleted, or formatted.
Tenorshare 4DDiG (Mac) also allows raw recovery, lost file recovery, and partition recovery. You can even recover data from crashed or dead Mac using the software.
Wondershare Recoverit For Mac
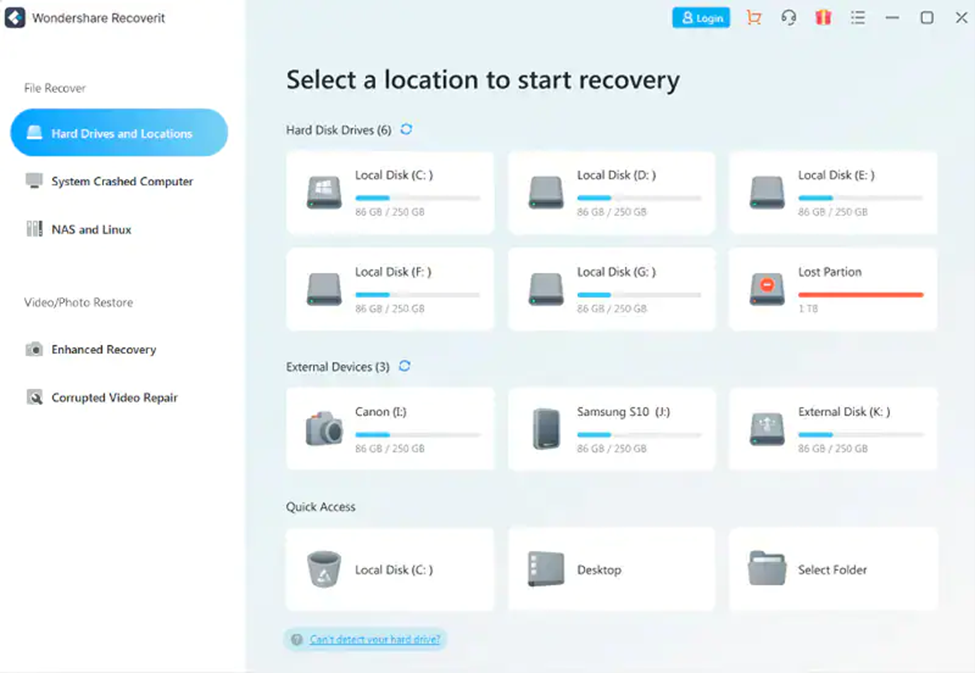 Using this software to recover your lost or deleted files on Mac is quite safe. You can recover lost office files, outlook & archive files, graphics, audio, videos, and more from internal and external HDD, SD cards, memory cards, USB flash drives, etc. Furthermore, you can even create a bootable media with the standard software version that helps recover data from a crashed Mac.
This software allows data recovery from a wide range of data loss scenarios such as virus attacks, accidental emptying of Trash, hard disk drive crash, factory reset with no backup, partition error, raw state, and re-installation of the operating system. The software supports different file systems, including APFS, ExFAT, FAT16, FAT32, HFS+, NTFS, Ext2, Ext3, Ext4, and more.
Using this software to recover your lost or deleted files on Mac is quite safe. You can recover lost office files, outlook & archive files, graphics, audio, videos, and more from internal and external HDD, SD cards, memory cards, USB flash drives, etc. Furthermore, you can even create a bootable media with the standard software version that helps recover data from a crashed Mac.
This software allows data recovery from a wide range of data loss scenarios such as virus attacks, accidental emptying of Trash, hard disk drive crash, factory reset with no backup, partition error, raw state, and re-installation of the operating system. The software supports different file systems, including APFS, ExFAT, FAT16, FAT32, HFS+, NTFS, Ext2, Ext3, Ext4, and more.
Softtote Data Recovery Mac
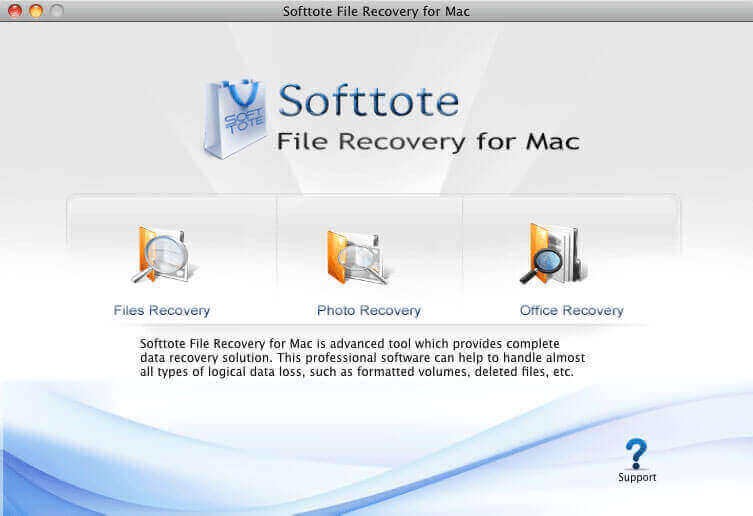 It is an all-in-one software for Mac data recovery that helps in retrieving lost or deleted files, missing partition and formatted drives. Not just this, the software is even capable of recovering data from corrupt HDD, camera, MP4 and MP3 player, USB Flash drive, etc.
The data recovery software also offers Photo Recovery, Lost Partition Recovery, and file recovery.
It is an all-in-one software for Mac data recovery that helps in retrieving lost or deleted files, missing partition and formatted drives. Not just this, the software is even capable of recovering data from corrupt HDD, camera, MP4 and MP3 player, USB Flash drive, etc.
The data recovery software also offers Photo Recovery, Lost Partition Recovery, and file recovery.
Data Rescue For Mac
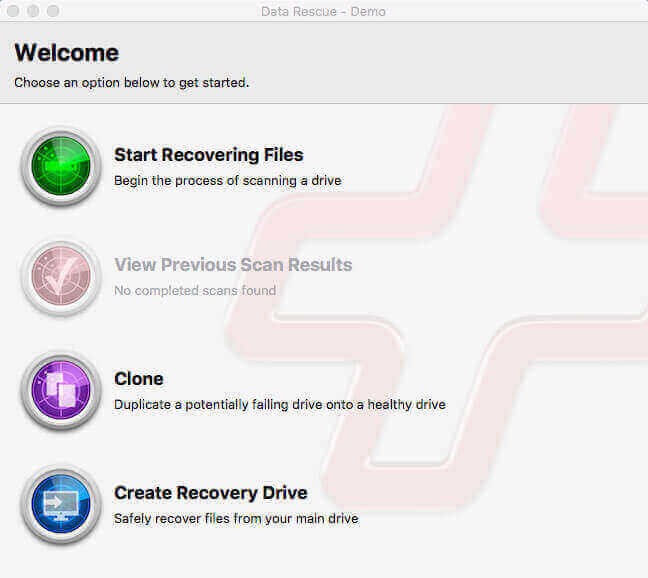 The function of this software goes beyond just hard drive recovery as it can also recover from different devices, like CF cards, SSDs, SD cards, USB drives, and many more. Using Data Rescue for Mac, you can easily locate, preview, and retrieve lost data, deleted files, and reformatted drives.
This software uses two scanning modes to scan your storage drive- Quick and Deep. It is possible to recover the files and view the previous scan results. You can recover photos, videos, audio, and various file formats.
The function of this software goes beyond just hard drive recovery as it can also recover from different devices, like CF cards, SSDs, SD cards, USB drives, and many more. Using Data Rescue for Mac, you can easily locate, preview, and retrieve lost data, deleted files, and reformatted drives.
This software uses two scanning modes to scan your storage drive- Quick and Deep. It is possible to recover the files and view the previous scan results. You can recover photos, videos, audio, and various file formats.
How To Choose The Best Data Recovery Software?
When deciding which software to pick for Mac data recovery, consider the data loss scenario at hand. Think what type of software will be able to bring back your files efficiently and in no time. There is a plethora of data recovery options available today. However, choosing the specific software that caters to your individual needs is a must for successfully recovering deleted files from Mac. Other factors while choosing the software can be the OS, file systems, data loss situations, and storage devices that the software supports. Another vital parameter to consider is the software’s ease of use; DIY software will be preferred much more than the ones requiring technical proficiency. Make sure to first download the trial version to preview the recoverable files. If you’re happy with the results, only then purchase the software. Look for the features in the software and figure out how they will benefit you. For instance- software with features like disk imaging, drive monitoring, and cloning can do wonders!Read Also :























