There are all kinds of businesses for which individuals have to fill out applications. You might have a banking app, for instance, and someone wants to fill out an application so they can purchase a CD or open a new checking account. You might have a website set up with a paywall, and some individual is trying to apply for membership.
There are many more business models where people try to fill out applications to become members, purchase things, get in line to buy new products coming out, and more. If they can fill out an application with no issues, it benefits them since they can get what they want, and it helps the business since it can generate revenue.
However, application fraud does exist, and it can harm a business entity significantly. In this article, we’ll explain what application fraud is, and we’ll go over some reasons it can devastate a business if that company can’t figure out a way to identify and block it.
What Exactly is Application Fraud, and Why Does It Happen?
There are all kinds of ways to block application fraud, such as AI machine-learning fraud protection. Before we talk about any of that, though, you should understand exactly what we mean when we use the term “application fraud.”
Application fraud occurs when a malicious individual or entity tries to sign up for a new account. They might do so on a website or through an app. They will usually use stolen or synthetic identities to do so.
They might sign up for a single fraudulent account, or they might create and run programs that try to activate hundreds or even thousands of new accounts at the same time. But why would anyone do that?
Profit is one reason. Someone might sign up for thousands of fraudulent accounts and then use the dark web to sell those activated accounts for a much lower price than the business would charge.
Mischief is another reason. Someone might try to activate all of those new accounts because they like destroying a company and tearing down what the business has tried to build. Some hackers are essentially anarchists, and they try to demolish legitimate businesses for no other reason than because they can.
Now, let’s examine three potential application fraud impacts.
A Company Can Lose Money When This Happens:
Let’s say that a hacker creates a program that tries to open thousands of new accounts at one time. The accounts they create give those who utilize them access to exclusive website content behind a paywall.
If the hacker is successful and sells those active accounts to dark web users, they will start using those accounts. The website, or site network, can potentially lose thousands of dollars or more. If they cannot generate revenue through legitimate, active accounts, then they may have to shut down eventually.
Their Site Can Crash:
A hacker might also create a program to try to open up lots of fraudulent accounts at the same time, and the website has safeguards in place that can identify and nullify the attack. However, the program might be so pernicious that it overwhelms the website’s defenses.
The hacker might not be able to get all of the active accounts that they wanted, but the company’s site can crash. When that happens, it might take their IT department several days to get it up and running again.
They Might Have to Pay for Tons of Overtime Hours:
In the scenario we just described, the company might have to pay their IT staff lots of money for the overtime hours they are putting in to get the website running once more. They might not even have a regular IT department, in which case, they will likely have to reach out to web developers or IT specialists via Upwork or some other freelancer platform.
This will ultimately cost the company money, and though they might have blocked the hacker’s attempt at stealing accounts, that hacker will have the last laugh. The company must still expend both cash and resources trying to bring their site back online.
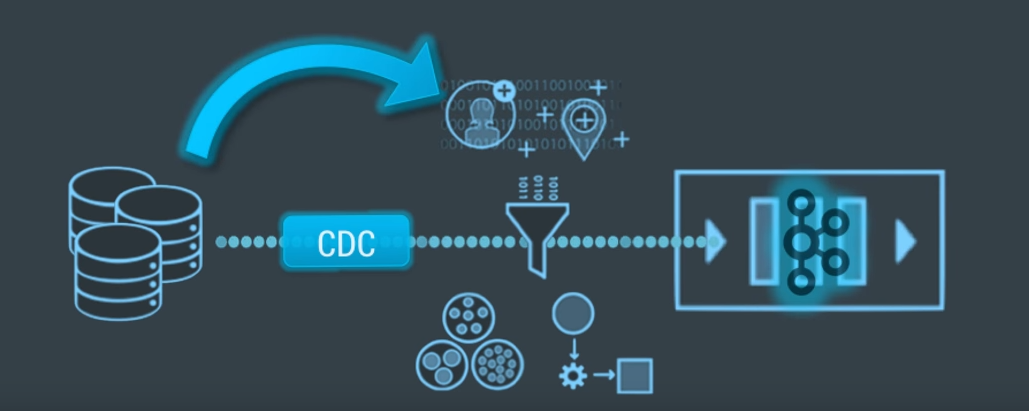
Application fraud can be problematic, but entities do exist that can help companies that are dealing with it. For instance, you can reach out to an entity that has AI-enabled software that can detect these attacks as they happen. They use advanced algorithms to zero in on the attack and stop it before it can go into effect.
The Role of AI in Detecting and Preventing Application Fraud
Application fraud is a problem that every business faces, regardless of size. Whether it’s a person using fake or stolen information to open an account or a hacker trying to create thousands of fraudulent accounts at once, the impact can be significant.
And Artificial Intelligence (AI) is helping businesses more effectively detect and prevent application fraud than ever before. But what is AI? And how does it stop fraud?
How AI Helps Prevent Application Fraud
Fraudsters often try to trick systems by creating fake accounts, using stolen identities, or running automated programs that generate multiple applications at once.
Traditional methods of fraud detection, like setting up rules that flag suspicious behavior (e.g., if someone opens multiple accounts in a short period), can catch some fraud, but they often fall short. Fraudsters are always coming up with new tricks to bypass these rules.
AI, on the other hand, also analyses but not according to strict pre-determined rules. It analyses real-time patterns and can catch even the tiniest of hastily hidden needles that may escape older systems.
Here are some ways how AI can stop application fraud:
Real-Time Detection
As applications come in, AI analyses them and looks for mismatched personal details. This could be within themselves or from other sources. For example, strange relationships between entities, strange activity, or use of synthetic identities (fake identities created based on stolen/made-up information).
Since AI can analyze fast enough, it flags these suspicions in real-time and helps companies shut down a fraudster before they have a chance to attempt fraud.
Recognizing Patterns of Fraudulent Behavior
AI learns from past incidents of fraud.
For example, if fraudsters often use certain email domains or apply for accounts at specific times of the day, AI can pick up on these trends and flag them in the future.
The more data AI systems are exposed to, the better they become at spotting fraudulent behavior, even if the fraudsters change their tactics.
Blocking Automated Fraud Attempts
Some fraudsters use bots (automated programs) to create thousands of fake applications in a short time.
AI can easily spot when an abnormal number of applications are coming in from a single source. Or, when bots are generating these applications based on behavior patterns that differ from human activity.
Once it’s been determined that fraud is occurring, AI can block these attempts so that you don’t have to deal with this type of fraud further down in your process.
Improving Over Time
AI’s biggest advantage is its ability to learn and improve. The more it is exposed to fraud, the more it understands new types of fraud.
Traditional methods require manual updates and are often redundant when confronted with evolving fraud.
Read Also: