Cybercrime cost businesses $3 trillion in 2015 and it’s expected to cost $6 trillion by 2021. A single cyberattack can ruin your online shop completely, so it’s essential to improve your eCommerce website security right away. Luckily, you can do this fast and with only a small investment.
How to Improve Ecommerce Website Security Quickly and Affordably :
1. Install security software :

Installing software that will monitor your website for SQL injection and other vulnerabilities is the first thing you need to do. SQL attacks (where hackers attach parts of SQL commands to your code) and malware are the most common types of cybersecurity hazards. These issues must be prevented at all costs, and a specialized security product will do that.
Such programs can guard you against a variety of attacks, so choose one with the widest range of protection. Be sure to invest in top-quality software updated frequently as new types of malware appear daily.
2. Switch to new hosting :
Are you 100% confident in the reliability and security of your hosting? If not, you should start looking for one that meets specialized e-commerce website requirements. The number one of those is having an SSL certificate, which is a proof of security.
Hosting matters greatly for an e-commerce website not only because of the cyberattack threats but also because uptime is essential for these businesses. If you use a shared server and it crashes every time traffic to your website surges, you’ll be losing business and ruining your reputation with customers. Today leading software providers offer many discounts and great terms for signup deals, so be sure to get the best one you can afford.
3. Switch to HTTPS :
A switch to a more secure protocol HTTPS is not only a way to improve e-commerce website security. It’s a necessary step if you want to rank higher on Google search engine result pages. The search engine assesses use this parameter when ranking your website, so using plain HTTP will lower your SEO.
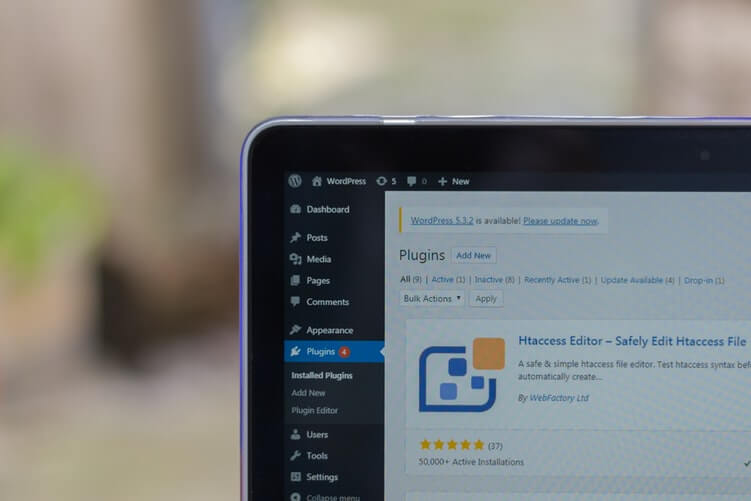
4. Keep all your plugins updated :
No matter how good your security software is, vulnerabilities might come from the inside if some of your plugins are old and don’t have the necessary levels of safety and performance.
The apps, plugins, and extensions on your website should update automatically. However, you should double-check in case some issue prevents an update.
Bear in mind that an old plugin is not only a security vulnerability. It’s also a risk factor for the website crash, which can lose you a lot of money.
5. Change your passwords and username often :
Hacking into your admin panel will give cybercriminals complete control of your business. To prevent it, you must have a strong password and a non-standard username. The latter you can change to anything you like.
As to the password, the best one should have no less than 20 symbols with letters in different registers, numbers, and symbols. Most importantly, it must be completely random.
Read Also :