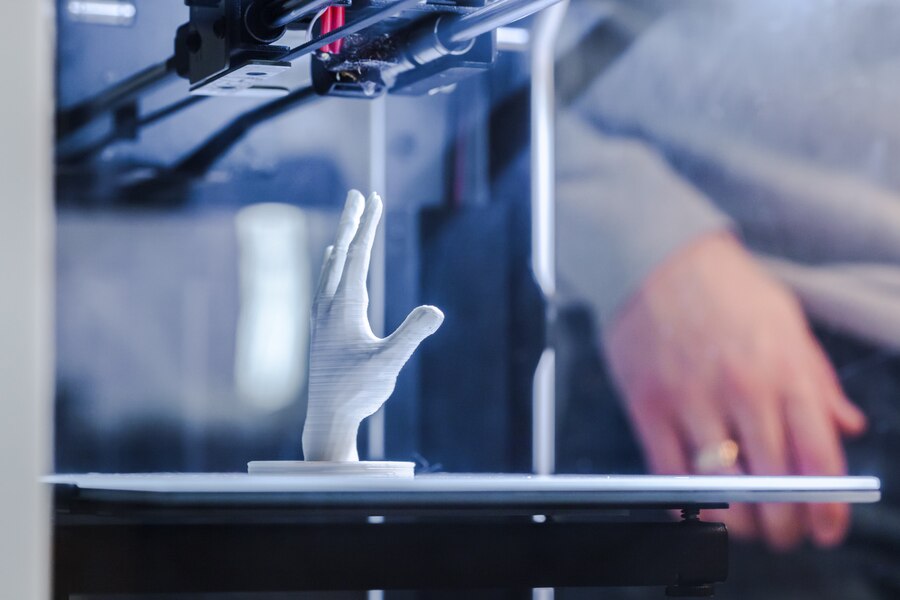
3D printing is manufacturing by constructing a three-dimensional object from a digital 3D model. Emerging technologies like 3D printing have brought revolutionary advancements in various industries, and the energy sector is no exception.
This article focuses on the techniques and applications of 3D printing in the energy sector, highlighting its potential to transform traditional manufacturing processes, optimize efficiency, and support sustainable practices.
Types Of 3D Printing Techniques For the Energy Sector
There are several techniques employed in 3D printing, including Fused Deposition Modeling (FDM), Selective Laser Sintering (SLS), and Stereolithography (SLA). Each plays a significant role in rapid 3D printing services. Here’s a detailed explanation of these 3D printing methods:
Fused Deposition Modeling (FDM):
FDM is the most famous 3D printing technique, where a thermoplastic filament is heated, and a 3D object is formed. FDM enables the production of complex shapes, intricate designs, and functional prototypes that improve energy systems.
Selective Laser Sintering (SLS):
SLM employs a high-powered laser to selectively fuse powdered materials, predominantly metals, generating durable and intricate components. This technique finds applications in manufacturing heat exchangers, turbines, and other robust energy system components.
Stereolithography (SLA):
SLA uses a liquid resin and solidifies it when exposed to a specific wavelength of light, creating precise and high-resolution objects. SLA produces custom-made energy storage systems, solar panels, and intricate electrical components for better energy utilization.
Advantages Of 3D Printing In The Energy Sector
There are several advantages of 3D printing, of which it has been in the leading demand. Some basic benefits are explained below:-
Cost Reduction:
3D printing allows the production of intricate and complex components in a single process, eliminating the need for assembly. It reduces manufacturing, increases efficiency, and lowers production.
Customization And Optimization:
The flexibility of 3D printing enables the customization of energy components based on specific requirements. By optimizing shapes and structures, energy systems can be designed for optimal functionality, resulting in enhanced performance and reduced energy wastage.
Supply Chain Sustainability:
Traditionally, energy systems rely on extensive global supply chains. Implementing 3D printing can reduce the dependence on transportation, minimize carbon footprints, and shorten lead times, contributing to a more sustainable energy sector.
Improved Efficiency:
3D printing enables the creation of lightweight components with intricate geometries, reducing energy consumption and improving overall system efficiency. This translates to enhanced energy generation, transmission, and storage capabilities.
Application Areas In The Energy Sector
3D printing is applicable in some areas in the energy sector as follows:-
Renewable Energy Components:
3D printing facilitates the production of wind turbine blades, 3d printed solar panels, and energy storage systems, allowing customized designs that maximize energy output and efficiency. Optoelectronic devices like photovoltaics and sensors can also benefit from 3D printing.
Energy Infrastructure:
3D printing for manufacturing pipes, heat exchangers, and valves reduces costs and enhances their resistance to corrosion, heat, and pressure. Advanced materials and designs derived from 3D printing contribute to safer and more reliable energy infrastructure.
Energy Efficiency Devices:
Customizable and intricate designs are made possible with 3D printing in developing energy-efficient devices like heat sinks, smart meters, and sensors. These technologies enable better monitoring, optimization, and management of energy consumption.
Tooling And Prototyping:
3D printing expedites the process of producing prototypes and specialized tools for testing and maintenance within the energy sector. This results in faster innovation cycles and improved productivity.
How 3D Printing Works
The basic steps which are followed by 3d printing are as follows:-
1. Submission Of Design:
The customer provides a 3D design file in a compatible format.STL or.OBJ, to the service provider. This design file can be created using 3D modeling software or downloaded from an online repository.
2. Pre-Printing Analysis:
The service provider examines the design file to ensure its suitability for 3D printing. They check for potential issues, such as intersecting geometries or unsupported overhangs, that may affect the printing process or the final result.
3. Material Selection:
Depending on the customer’s requirements and the properties desired for the object, the service provider suggests suitable materials for the 3D printing process. Options can include various plastics, metals, ceramics, or composite materials.
4. Printing Process:
Once the design and material considerations are finalized, the 3D printing process begins. The service provider prepares the 3D printer, loads the selected material, and starts printing. The printer follows the instructions in the design file to layer the fabric and create the desired object.
5. Post-Processing:
After printing, the printed object is typically subjected to post-processing steps. It may involve removing support structures, cleaning the thing, or applying surface finishes to achieve the desired texture, color, or smoothness.
6. Quality Assurance:
The service provider examines the printed object for defects or imperfections and ensures it meets customer requirements. If necessary, adjustments or corrections can be made before final delivery.
Conclusion
Integrating 3D printing techniques within the energy sector presents transformative opportunities for manufacturing, sustainability, and energy efficiency. The ability to customize designs, reduce costs, optimize efficiency, and shorten production timelines can revolutionize energy generation, transmission, and storage.
As this technology evolves, a collaboration between 3D printing experts, energy specialists, and researchers will lead to further breakthroughs, fostering a more sustainable and efficient energy future.
Read Also:
- Advance Copier: Printing Quality Business Cards On Your Own Computer
- 7 Ways To Stop Spending So Much On Printing In Your Business
- Digital Printing Contributes Much Towards The Progress Of The Industry