Are you searching for information about the Google Verification Code scams? If your answer is a YES, then you are not alone in this.
While it is true that in today’s age of technology and technical advancements, things have become much easier and faster, there is yet another thing that is true. And it is a fact that there is an increased amount of negative actions like frauds and scams that people are having to face and deal with.
One of the most haunting things that is happening right now is the Google Voice Scam or verification code scam. If you have faced it or want to know the best ways to deal with it, you will find this blog to be of help. Keep reading this article till the end to learn more…
What Are Google Verification Code Scams?
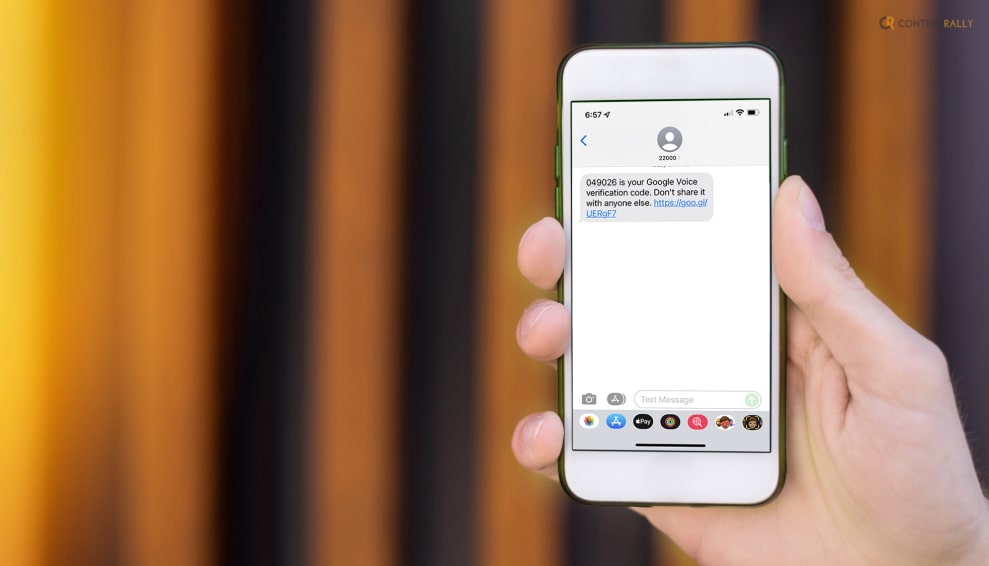
Google verification code scams are fraudulent activities where scammers attempt to deceive individuals into providing them with a Google verification code. These scams often occur through various channels such as email, text messages (SMS), or phone calls.
Also known as Google Voice Scams, this is something that most people have complained about. Consumers purchasing goods or connecting with new friends on the internet may be coerced into using the alternative online phone service, and that is where the fraudulent activity begins.
How Do Google Verification Code Scams Work?

In case you want to know how this scam takes place, I have you covered. Here is a detailed description of how this scam works:
1. Initial Contact
Scammers may initiate contact through an email, text message, or phone call, claiming to be from a reputable organization or service provider, including Google. They might use tactics like urgency or fear to convince you to take immediate action.
2. Deceptive Message
The scammer usually sends a message that suggests there is a problem with your account or that you’ve won a prize or lottery. They may claim that your account has been compromised or that you need to verify your identity to prevent unauthorized access.
3. Request For Verification Code
To proceed with the scam, the scammer will ask you to provide a verification code they claim has been sent to your phone number. They may state that this is a security measure or part of the verification process. In reality, they want to gain access to your account.
4. Social Engineering Tactics
Scammers often employ social engineering techniques to manipulate you into revealing the verification code. They may use persuasive language, impersonate customer support representatives, or create a sense of urgency to pressure you into sharing the code.
5. Unauthorized Access
If you unknowingly provide the scammer with the verification code, they can use it to gain access to your account, potentially allowing them to steal personal information, commit identity theft, or engage in other fraudulent activities.
Why Is There An Increase In Google Verification Code Scams?

Why would someone send me a google voice verification code to scam me? Well, this is truly one of the most asked questions related to this fraudulent behavior.
Google verification code scams and other forms of phishing attacks have been a persistent threat over the years. Cybercriminals adapt their tactics to exploit new vulnerabilities and trends, making it challenging to provide specific growth statistics. However, it is widely recognized that phishing scams, including those involving Google verification codes, continue to be a significant concern for individuals and organizations.
Here are a few factors that contribute to the growth of these scams:
1. Increased Reliance On Digital Services
As more individuals and businesses rely on digital platforms and services, scammers have more opportunities to exploit vulnerabilities and trick people into revealing their personal information.
2. Social Engineering Techniques
Scammers employ sophisticated social engineering tactics to manipulate victims into providing verification codes. They use psychological manipulation, urgent language, and impersonation techniques to gain trust and deceive unsuspecting individuals.
3. Availability Of Personal Information
With the prevalence of data breaches and leaks, scammers may already have access to some of your personal information. This information can make their phishing attempts seem more credible and convincing.
4. Mobile Device Usage
As mobile devices become more prevalent, scammers have shifted their focus to target users through SMS-based scams. This includes attempts to trick individuals into sharing Google verification codes received via text messages.
5. Global Nature Of Scams
Google verification code scams are not limited to specific regions or countries. They can originate from anywhere in the world, making it difficult to enforce laws and track down the perpetrators.
How To Protect Yourself From Google Verification Code Scams?

To protect yourself from Google verification code scams, it is crucial to remain vigilant and follow these guidelines:
1. Be Cautious
Exercise caution when receiving unsolicited messages or calls that request personal information or verification codes. Be skeptical of urgent or alarming requests.
2. Verify The Source
If you receive a message claiming to be from Google or any other organization, independently verify its authenticity. Contact the company using official contact information to confirm the message is legitimate.
3. Enable Two-Factor Authentication (2fa)
Set up 2FA for your Google account and other online services whenever possible. This provides an additional layer of security by requiring both a password and a verification code to access your account.
4. Protect Personal Information
Avoid sharing sensitive information such as verification codes, passwords, or account details with anyone unless you have independently confirmed their identity and legitimacy.
5. Report Suspicious Activity
If you encounter a Google verification code scam or any other form of fraudulent activity, report it to the appropriate authorities and the company being impersonated. This helps raise awareness and protects others from falling victim to similar scams.
What Does Google Say About Protecting From Google Verification Code Scam?

When you sign up for Google Voice or add a phone to your account, Google sends you a text message with a verification code. You enter this code to activate Voice on your phone. However, there are times when you can face fraudulent statements.
Here are some of the things that you can do to protect yourself from this scam:
1. Don’t Share Your Verification Code With Anyone
It is essential that you do not respond to any requests for your verification code in order to prevent unauthorized access to your account. This code will never be requested by Google employees. Keep in mind that your Google Account’s security is absolutely necessary.
2. Disconnect Your Number From Google Voice
Disconnect your phone line if you want Google Voice to stop using your phone number. Your number can be disconnected if:
- You have been duped into providing your verification code even though you are not a Google Voice user.
- You don’t want Google Voice to forward calls to you.
Wrapping It Up!
In case you were searching about Google verification code scams, I hope that this article has been of help to you. If there are any other queries related to the same, feel free to let me know. All that you need to do is scroll down till you reach the bottom of the page. Then leave your queries and suggestions in the comments box below. And I will be there to answer them all for you!
More Resources:
- How to Set Up Business in the DMCC Free Zone?
- Dos And Don’ts Of Marketing For Technology Companies
- Why Is Google Sucks Trending? Top Reasons And Justifications























